Account takeover happens every day. It’s not enough to safeguard account access at login.
BioCatch’s Account Takeover Protection leverages multi-threaded fraud telemetry synthesized with behavioral intelligence to continuously analyze more than 14 billion digital banking sessions every month, detecting subtle anomalies in real time across web and mobile channels.
Account takeover tactics evolve. Access is exploited. Credentials are compromised.
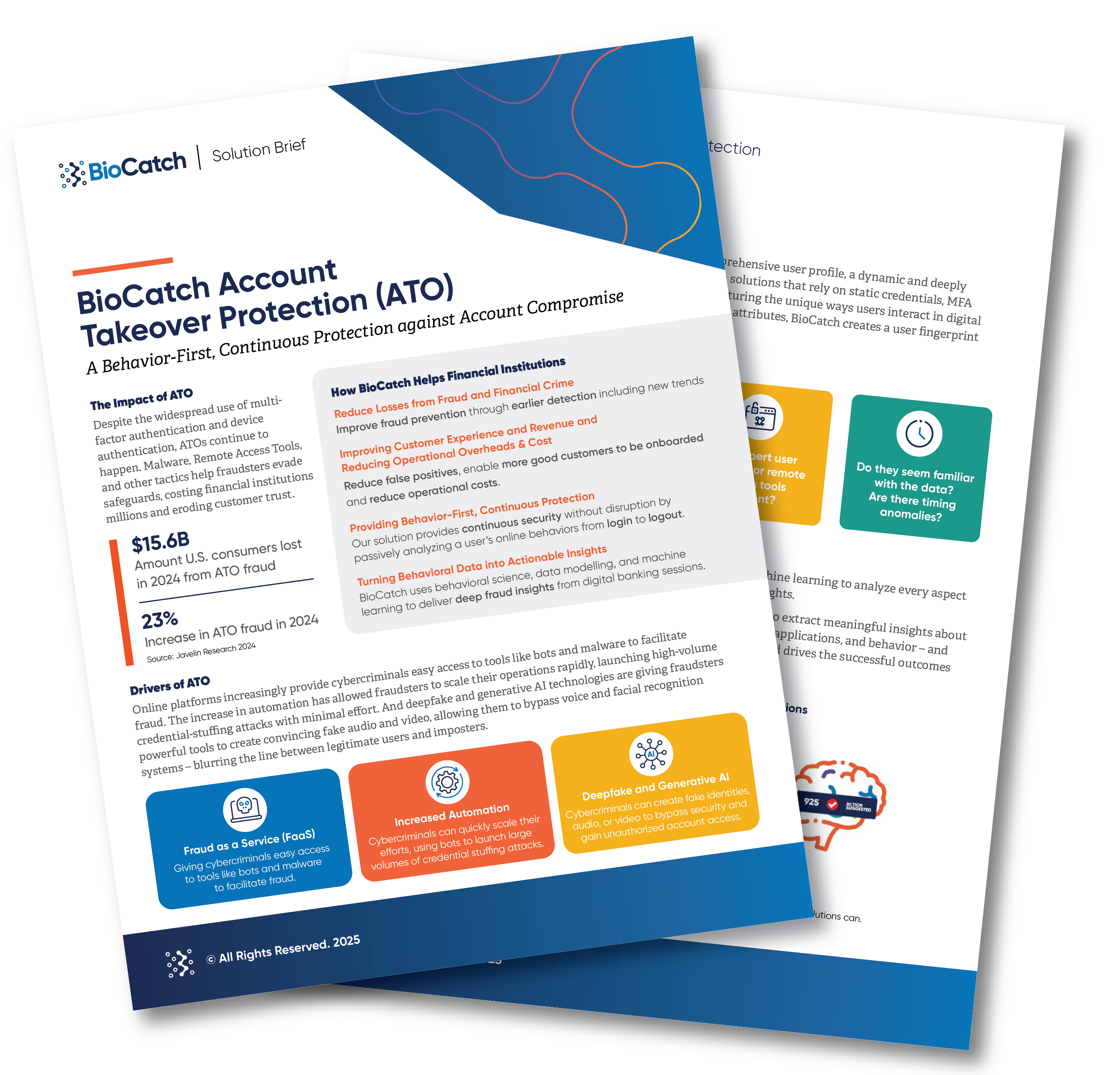
Cybercriminals use a wide range of tactics to gain access to online banking accounts — from harvesting credentials through phishing attempts to manipulating users into unwittingly surrendering confidential information.
Proven results
Continuous telemetry, behavioral sequencing, and predictive analysis underpin BioCatch’s Account Takeover Protection solution, detecting anomalies between expected and observed behaviors to isolate takeover attempts and prevent monetary losses — all while ensuring an uninterrupted customer service.
66%
increase in fraud-detection rates at one LATAM bank
95%
reduction in Zelle fraud losses at a major U.S. bank, just two months after integrating our ATO solution
54%
ATO attacks that involved a changed password or email address
92%
account takeover fraud that happens on mobile devices