It seems everywhere today, people are talking about being in the midst of a global epidemic of digital scams targeting victims from all directions. But I’ve noticed that no one is providing an explanation as to why scams – which are usually nothing more than a technology enabled version of an old-fashioned confidence scam (or grift) – have become the dominant fraud type.
I’ve been involved in digital fraud prevention for almost 20 years now, and I have seen attacks evolve in response to bank controls alongside regulatory changes. Most of my working life has been in the UK, which has been at the tip of the spear for many attacks, but it has also taken me further afield into the United States, Australia, and several other countries.
From this perspective, I can see certain commonalities and regulations which have driven the threat landscape – which I think starts to explain why we are now in the position we are in. The UK was the first market to see scams overtake other traditional forms of fraud and gives us all the data points we need to understand the bigger picture.
In my mind, no single event was truly responsible for the rise of scams (of whatever type). Fraud attacks have evolved over the past two decades in response to both the pull of business changes and the push of the changes in threats. The balancing act between the two caused the evolutionary pressure leading to the “scampocalypse” we see today. 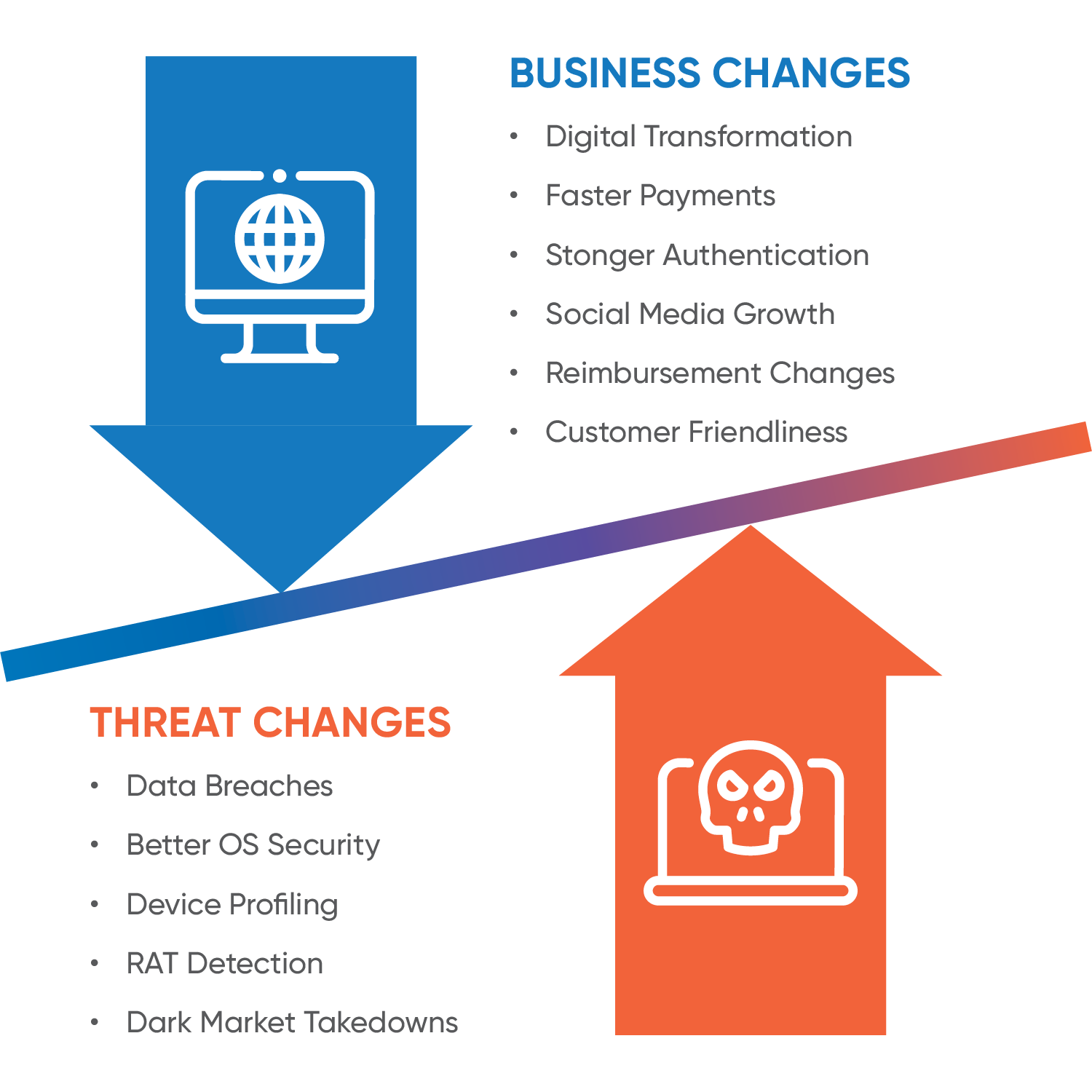
Here are the five factors I believe that have contributed to the global scampocalypse.
Factor 1: Uniformity Due to Regulation
Mandatory regulatory and legislative changes create consistency across all banks in a region so attackers face the same challenges no matter which bank they attack. Once attackers have an MO that works for any bank in a region, they will attack all banks who are susceptible to it. They move on to other banks only when stronger controls are put in place and focus their attacks on those that have weaker controls.
For example, in EMEA, the Payment Services Directive 2 (PSD2) mandated Strong Customer Authentication (SCA), increasing two-factor authentication to three (Possession, Inherence and Knowledge). In retrospect, this requirement has not really reduced fraud losses and has increased customer friction – and even discriminated against vulnerable customers due to the complexity of the authentication solutions deployed.
Factor 2: Business Changes
Several changes on the business side can be directly tied to the increase in scam activity including:
- Digital Transformation: Banks have worked quickly to move services online to meet demand for digital banking, both on the web and on apps. Along with this change comes higher payment limits and capabilities, physical branch closures, and increasing attacks against customers now limited to online banking only.
- Faster Payments = Faster Fraud: Attackers can rapidly try multiple ways to get around the defender controls, and faster payment rails are a sweet spot. With instant payments, they no longer need to wait overnight or multiple days to see the results of their crimes. Payment and cash out can be performed in mere seconds.
- Stronger Authentication: With regulations such as PSD2 SCA, 100% of fraud is within strongly authenticated sessions, so attackers now must circumvent SCA measures via technical or social engineering means.
- Social Media Growth: Social media enables unprecedented global communication but it also opens the door for criminals. Recently, financial giant, Barclays, reported that social media is the source of 87% of scams. People overshare personal data: It is no longer clear as to what is an advertisement and what is user-generated. There are echo chambers of beliefs across multiple messaging channels (SMS/WhatsApp/Messenger/Tiktok etc); People are confused as to what is a legitimate bank message and often reply immediately to requests that seem urgent or critical. In addition, young people are savvy message app users (SMS, chats, app messaging, WhatsApp, etc.) which makes it easier for them to pretend to be someone else, especially with powerful new tools like ChatGPT.
- Reimbursement Changes: Recent developments in consumer reimbursement, such as the requirements released by the UK Payment System Regulator (PSR), now make it less onus on the customer to even spot a scam, which may result in them paying less attention to potential scams.
- Customer Friction vs. Security: As banks try to make their website, mobile apps, and procedures customer friendly, they often inadvertently make them fraudster friendly too. For instance, the more customer friendly it is to register a new mobile device, the easier it is for fraudsters to do so. The same for password resets: It is bad for a genuine customer to get locked out, but the reset is often used by fraudsters to get in.
Factor 3: Threat Landscape Changes
As business have changed, the threat landscape has changed in multiple ways as well.
- Data Breaches: Data breaches result in freely available information about a vast percentage of a country’s population. With these breaches come compromised emails, usernames, and passwords and the ability for criminals to search and profile by age, account balances and susceptibility/vulnerability of the victim.
- Improved OS Security: As it is now more difficult to infect victim systems with malware or to show phishing sites within browsers, criminals rely on scams as technical attacks became more difficult to deploy over time.
- Device Profiling: Similarly, it is now harder to impersonate victim devices, even if the victim’s account details and type of devices used is known.
- RAT Detection: Remote Access Tools (RATs) deployed to bypass device profiling controls are now being flagged when used by technical scans or behavioural changes.
- Dark Market Takedowns: It is no longer easy for bad actors to purchase technical criminal tools, such as malware, criminal RATs or other methods of bypassing detection due to the cost of tools going up and only being available to a small number of trusted buyers.
Factor 4: Change of Attackers
Attackers have drastically evolved in the last two decades as technology advancements have enabled more automation and specialisation within fraudster communities.
- Typical Early Attackers: Fraudster skillsets have changed. In the past, fraudsters often possessed high technical capabilities, undertook entire attack kill chain themselves, possessed lower foreign language capabilities, and operated in lower numbers. They could automate attacks by technology, such as creating malware or botnets.
- Typical Current Attackers: Conversely, they now often possess lower technical capabilities and focus on specialisation across the attack kill chain (e.g., emails, voice calls, cashout and money laundering), have higher local language capability, and operate in higher numbers. They can now operationalise attacks by outsourcing and throwing more (low cost) bodies at a problem to scale.
- Future Attackers: Criminals will most likely increase their technical capabilities enabled by access to AI, resulting in higher financial ability, even higher numbers than today. They might also operationalise attacks through a combination of people and AI.
Note: This generalisation does not include the Nation-State type attacks conducted for financial reasons as they are a specific subtype that is more of a Black Swan attack – low probability but high impact.
Factor 5: Wetware Became the Weakest Link
From these four factors, we see that in order for digital banking fraud to succeed, attackers must get around strong authentication – but the technical measures to do this were harder to obtain and often needed social engineering to install them. So why invest in technology and complexity when fraudsters can just use low-cost people instead?
Criminology looks at three factors to determine how likely a criminal attack will occur – risk, reward, and effort. Scams, starting with the bank impersonation scams, needed a phone call to the victim who is then guided to move money themselves. This took more effort than using a technical solution in terms of time, but data breaches already provided all the information on victims needed to scam them. But more importantly, the risk in doing so was lower (less technical footprints during the fraud), and the reward was much higher initially (technical controls such as authentication, device profiling, and transactional analysis gave high false positives, and behavioural biometric analysis was still in its infancy).
Ultimately, criminals conducted sophisticated attacks against the weakest point – the bank customer – as humans became the simplest and best chance at beating the bank controls. Once one attacker group proved it worked and word spread, fraudsters around the world copied them to generate the high volumes seen now.
The Future Is Human
Voice scams, such as impersonation of banks or law enforcement, were the first wave of the scampocalypse, with customers naively believing what they were doing was correct. Today, voice scams are still a big issue. What started out mostly in the UK and spread to the rest of the English-speaking world is now a problem across all regions and languages. For instance, fraudsters invest in native speakers to provide the authenticity they need and now use the same methodology across Europe and Latin America. These regions are seeing the shift from account takeover due to the same technical control improvements the UK was first to implement.
As the UK has shown, behavioural analysis of the customer during these impersonation scams, when layered with transactional controls, has the ability to reduce the reward of the attackers (and means their effort does not scale). More work needs to be done on increasing the risk to attackers, but effort is underway to uncover mule networks and identify where the stolen money is going to. Law enforcement, such as Europol, has already done a lot of work on money mule disruption, and this is likely to increase over time as more data is correlated.
We must not forget the other types of scams that are also out there – purchase, romance, crypto/investment and others. Again, these focus on the human victim, without the technical signals we once relied on for account takeover being present. Behavioural and transactional signals are now the key battlegrounds to spot these, but the focus has now shifted to looking at them at the receiving account as much as the sending.
There are additional viable behavioural signals on the mule side which until recently have been under-utilised. Linking both sides of the transaction gives better accuracy, and when done correctly, reduces the operational cost of both the sending and receiving bank. FRAML (Fraud and AML) operational teams are more common now, and in some cases, cyber fusion centers link infosec teams as well.
My parting thoughts are that with this retrospective view of the combination of factors that caused the threat landscape to shift, we can predict how other verticals outside of banking –insurance, government gateway services, gaming/gambling, eCommerce – are vulnerable to the same attack shift due to similar factors in play. My advice to these industries is to learn from the painful lessons and new capabilities that have come from the banking sector before a scampocalypse overwhelms you.
Additional Resources
Discover additional resources related to the topic of social engineering scams below:
White Paper: On the Precipice of the Scampocalypse
Analyst Report: Fraud Organizational Structures: Progressing Toward a Holistic Financial Crime Corporate Strategy



