BioCatch blog channel
Browse topics
- Fraud
- Social engineering scams
- Fraud Prevention
- Money Mules
- Mule Accounts
- Authorized push payment scams
- Behavioral intelligence
- Payments
- Account takeover
- Social Engineering
- Financial crime
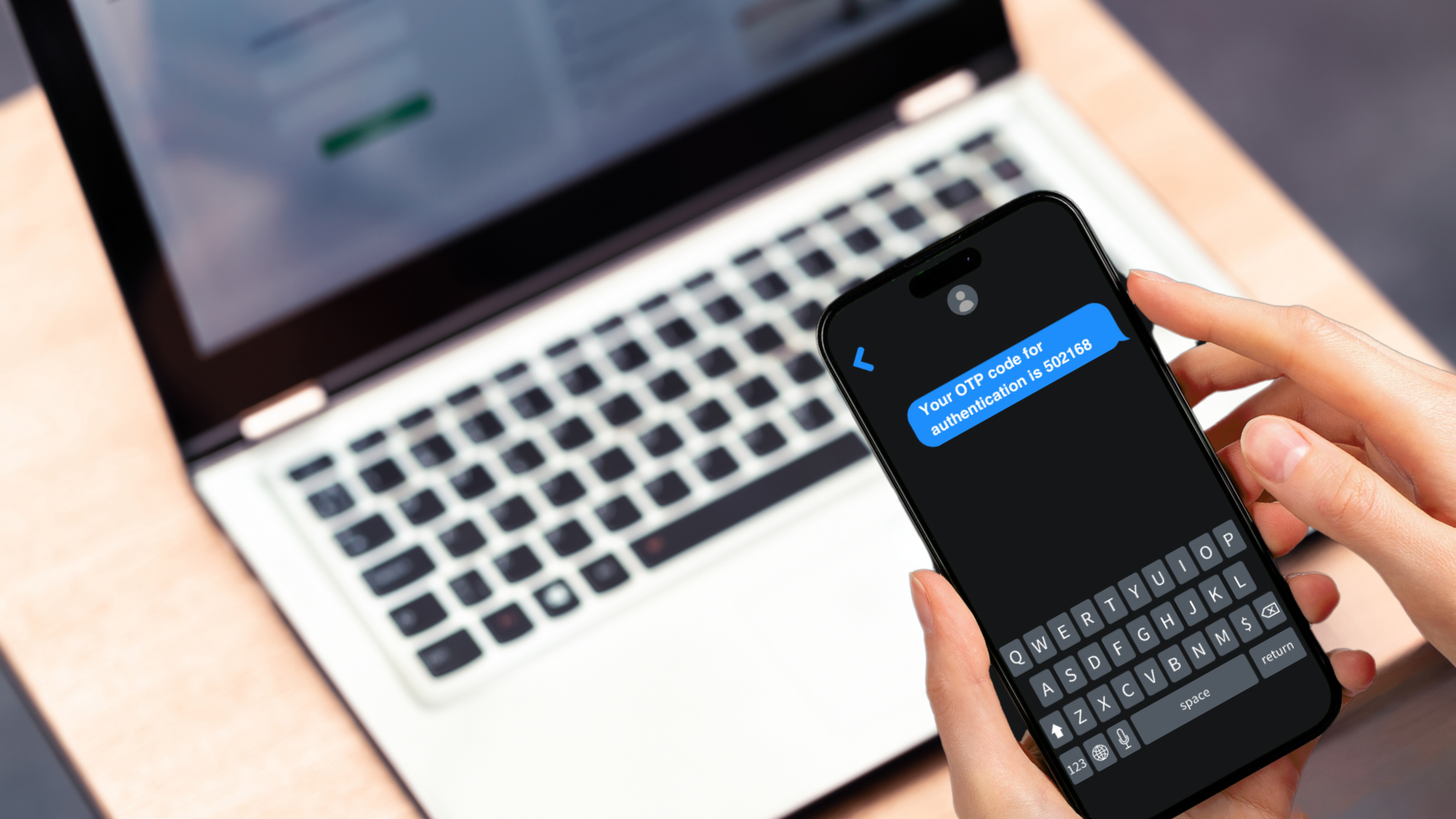
- Authentication
- New Account Fraud
- Fraud Detection
- Impersonation Scams
- Anti-money laundering
- Featured
- Banking / Financial services
- Continuous authentication
- AI
- Malware
- ROI
- authorised push payment scams
- investment scams
- Authorised push payment fraud
- BioCatch Team
- Connect Buenos Aires
- Connect Europe 2025
- Connect London 24
- Connect NY
- Community
- Continuous Protection
- Cybersecurity
- Identity Proofing
- account opening experience